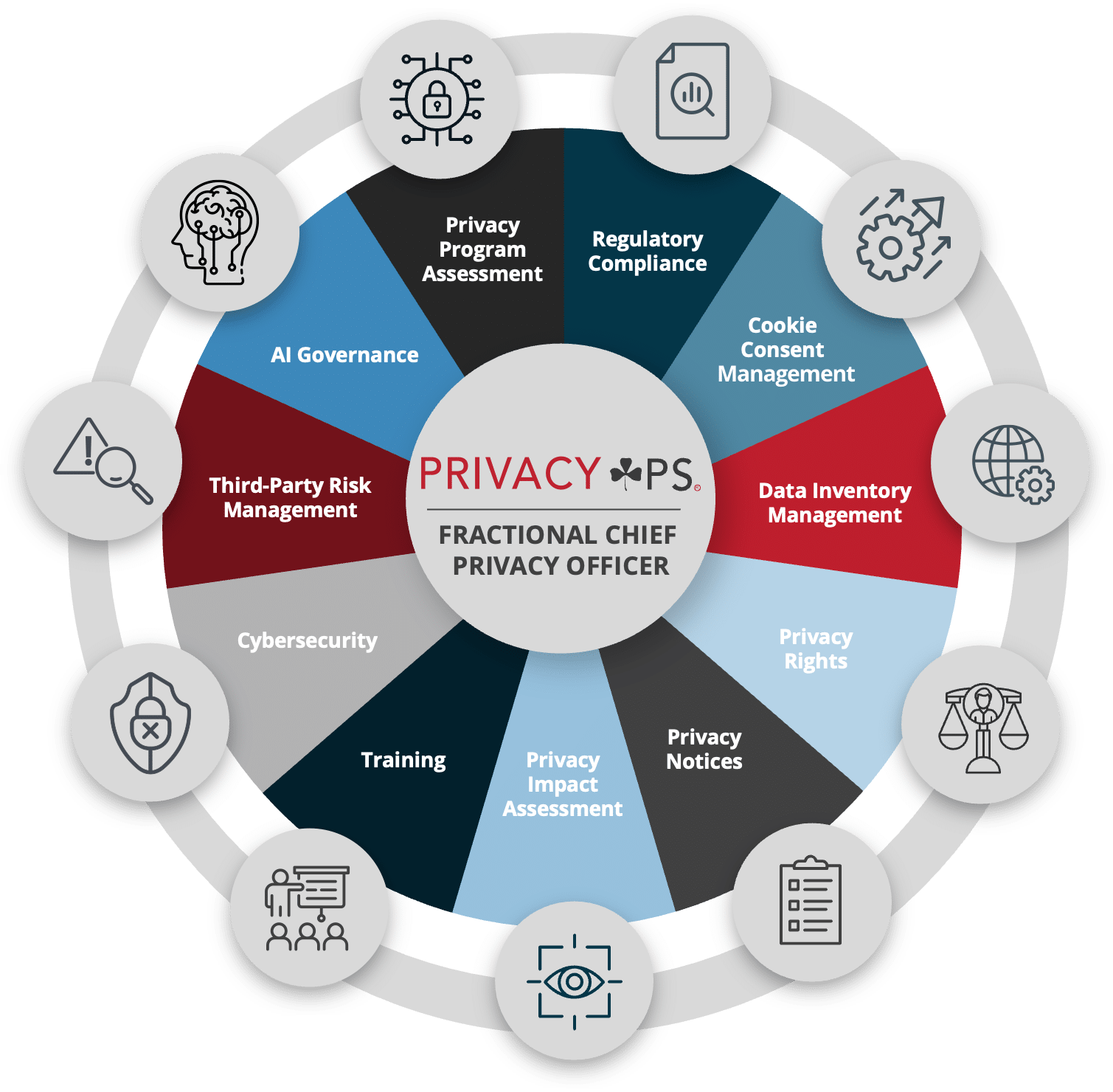
Our goal is to provide assurance in managing privacy operations across all fronts.
Privacy management is complex. Because it touches all aspects of a business, a comprehensive approach to privacy is essential for meeting compliance demands effectively. It’s a heavy lift — and that’s where we come in.
What is Privacy Operations?
Privacy operations are the nuts and bolts of privacy programs. This includes the technologies, processes, procedures, and policies organizations use to build and maintain data privacy programs. While privacy needs are different for every organization, privacy operations can be tailored to fit specific business needs to manage data responsibly, streamline compliance efforts, reduce risk, and boost customer trust.
How Can Red Clover Help Your Organization?
See how we’ve helped other companies like yours.
Explore our client testimonials and case studies to see how we help our customers stay compliant while driving meaningful results.